Security CV Examples
Start creating your CV in minutes by using our 21 customizable templates or view one of our handpicked Security examples.
Join over 260,000 professionals using our Security examples with VisualCV. Sign up to choose your template, import example content, and customize your content to stand out in your next job search.

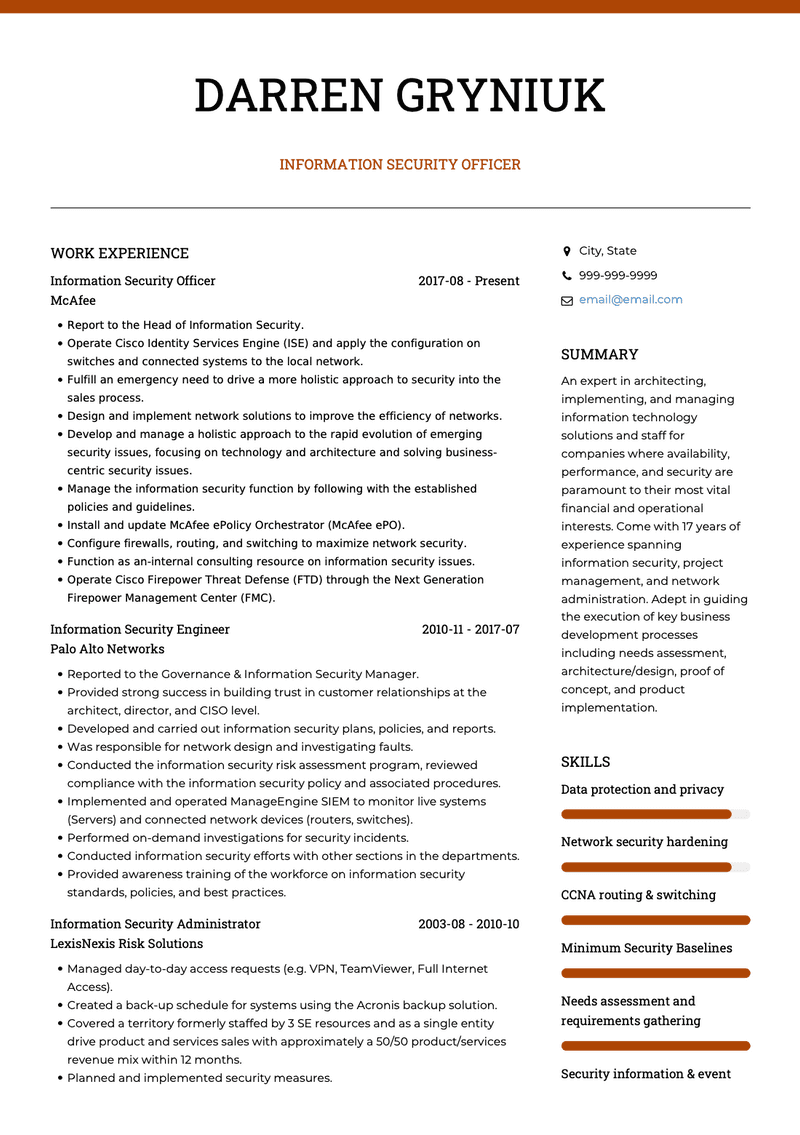
Information Security CV
SUMMARY
Detail-oriented, highly skilled Information Security Specialist with 14+ years of expertise in information technology including risk management, system hardening, and malware prevention, detection, and removal. I pride myself to learn from every experience and apply my knowledge/experience fully in all areas to push boundaries. Able to flourish in a fast-paced, exciting environment where precision and productivity matter. I have been well versed in the security and technology field of the US and hope to continue my momentum to make a substantial impact on the improvement of business and technology systems.
WORK EXPERIENCE
CROWDSTRIKE
Information Security Specialist
- Manage the contents of the organization’s risk register and carry out tasks regarding risk treatment.
- Implement of MSBs in all ICT software/Hardware where applicable.
- Engineer policies and facilitate the implementation of Cisco Identity Services Engine.
- Define and manage industry Security and Standards Roadmaps ensuring industry security posture.
- Review and approve end-user requests for application installation and internet access.
- Implement Cisco Umbrella formally OpenDNS (Replacing Cisco Ironport Proxy).
- Manage industry projects to migrate cryptography mechanisms ensuring industry-wide and international interoperability.
- Design safeguards around wire fraud phishing emails.
- Monitor compliances with security policies.
SECUREWORKS
Information Security Manager
- Managed and implemented multi-factor authentication.
- Performed on-demand investigations for security incidents.
- Managed the Tenable Security Center and maintain vulnerability assessment plan.
- Designed firewall changes workflow for approval and change execution.
- Ensured frameworks and security are aligned with global best practices for authentication, cryptography, and privacy.
- Checked rules and configuration of DLP in the end-user computer, examines DLP logs, and takes appropriate action.
- Managed Symantec Endpoint Protection 14 policies and oversee the operations.
- Advised industry security committees on security best practices and current vulnerabilities. Continually review industry security guidance and rules, aligning rules to industry best practices.
- Analyzed current trends in malware and the organization’s current controls to determine whether advanced malware protection (AMP) tools are warranted.
- Implemented Ironkey encrypted USB storage.
INFOBLOX
Information Security Analyst
- Collaborated and maintained ongoing security policies and controls to strengthen NBTY’s security posture.
- Reviewed and monitored vendors based on SLA.
- Developed endpoint firewall policies for our UK retail environment.
- Was responsible for Internet proxy configurations, policies, and reports.
- Maintained ATM and EFTPOS network processing and monitoring systems.
- Created security metrics and reports that management uses to understand the effectiveness of their security systems.
- Created documentation to assist associates with the enrollment of security services.
- Reviewed information security policy and make changes if applicable.
- Controlled endpoint security utilizing Symantec Endpoint Protection in a global environment.
EDUCATION
HARVARD UNIVERSITY
Master of Computer Science
UNIVERSITY OF CHICAGO
BSc (Hons)-Bachelor of Science
- Computer Science & Cybersecurity
SKILLS
- DATA LEAKAGE PREVENTION
- CRYPTOGRAPHY
- WARNING SYSTEM & TECHNOLOGY THREAT
- ENDPOINT PROTECTION
- Symantec Endpoint Protection
- POLICY CREATION
- Creation of Information Security Policies
- SECURITY AWARENESS
- Delivering security awareness training to associates
Copyright ©2024 Workstory Inc.